Since electronic health records (EHRs) have become industry-standard in healthcare, keeping the data contained in EHRs secure is never an option to neglect. Patient personal data leakages, security breaches of healthcare organizations’ databases, and unauthorized access to confidential EHRs can entail not just expensive audits but far greater troubles for any healthcare service provider.
In this article, we will share some valuable insights regarding the security and privacy of EHR development that we’ve acquired throughout the years of firsthand experience in the field, discuss ehr return on investment, and the major EHR development security issues, and how to address them.
EHR Privacy and Security Issues
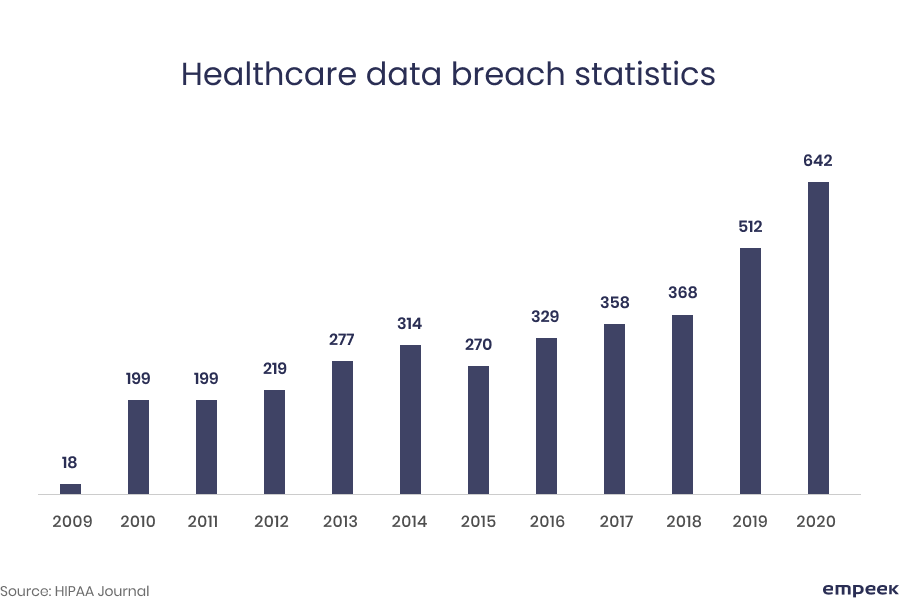
Despite the rapid technological advancement, EHR&EMR systems remain heavily vulnerable to security breaches. There are different types of emr software. Over the last decade, almost 3 million medical records have been disclosed, lost, or stolen in the US. It means that nearly one out of ten US citizens experienced exposure to their medical data at some point in time.
Mismanagement of electronic medical records is a common issue resulting in data breaches. It is estimated that 77% of data breaches have been caused by healthcare organizations, which means there is a strong need for medical institutions to focus on reinforcing data security and protection measures.
As data-science specs say, every connected device is potentially hackable. EHR security and privacy concerns follow this way of thinking. Thus, all chip-driven devices used at a healthcare organization, be it desktop computers, tablets, or even smartphones, should be equated with the special medical equipment capable of having a direct effect on patients.
Why Confidentiality in Healthcare is Crucial
There are different types of EHR software. Data breaches are not only expensive and budget-undermining, they also spawn many other risks related to corporate reputation, performance, etc. Let’s take a look at some particular examples.
Reputation
The actual harm they cause to healthcare organizations is not about the database price. The very fact that some sensitive patients’ data has been lost can be enough to ruin both the reputation of a local healthcare authority and the privacy of many people.
For example, a Bluecross organization Excellus leaked sensitive info of over 10 million hospital and military clinic patients, which made it immensely difficult to win its customers’ loyalty back. Likewise, UCLA got over 4.5 million patient records exposed in 2015 and was harshly criticized for not encrypting personal healthcare data in the first place.
Extra pressure during the pandemic
The COVID-19 pandemic put immense pressure on the healthcare systems all over the world. With a growing demand for health care services, EHR privacy and security issues became even harder to handle, let alone a number of other issues and challenges that medical institutions faced in the wake of the pandemic.
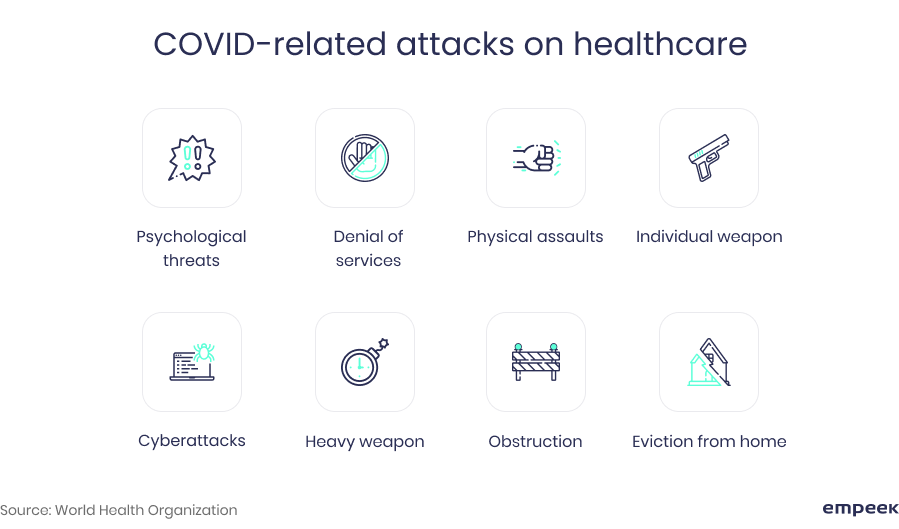
With consideration of all these issues, it would be fair to say that those organizations that had a strong data protection strategy in place beforehand were able to respond to other emerging pandemic-related challenges more efficiently.
Patient confidentiality laws
There are global privacy regulations, including HIPAA, HITECH, and other laws, breaching which is a criminal case. Undermining doctor-patient confidentiality can result in a number of allegations concerning human rights, personal privacy, and data protection.
The US Department of Health and Human Services has a special portal in place dedicated to compliance breaches. Named as Wall of Shame, it is dedicated to the most relevant data breach cases, tendencies, and related names. The strongest argument here is that a single penalty may go beyond $1 million per year, and these penalties are added up and accumulated over time.
Extra costs
The EHR mismanagement leading to data breaches costs healthcare providers too much in every possible way. IBM report states that an average cost of healthcare data breach reaches up to $7 million, and this number is growing. Solving legal problems is never cheap on top of the fact that you will have to find a way to urgently reinforce the existing data security measures.
Major Threats to EHR Security
Medical devices applied to both diagnostics and treatment are highly computerized these days. Some malware or a virus can make a heart-rate monitoring system useless, spawning risks to a patient’s life.
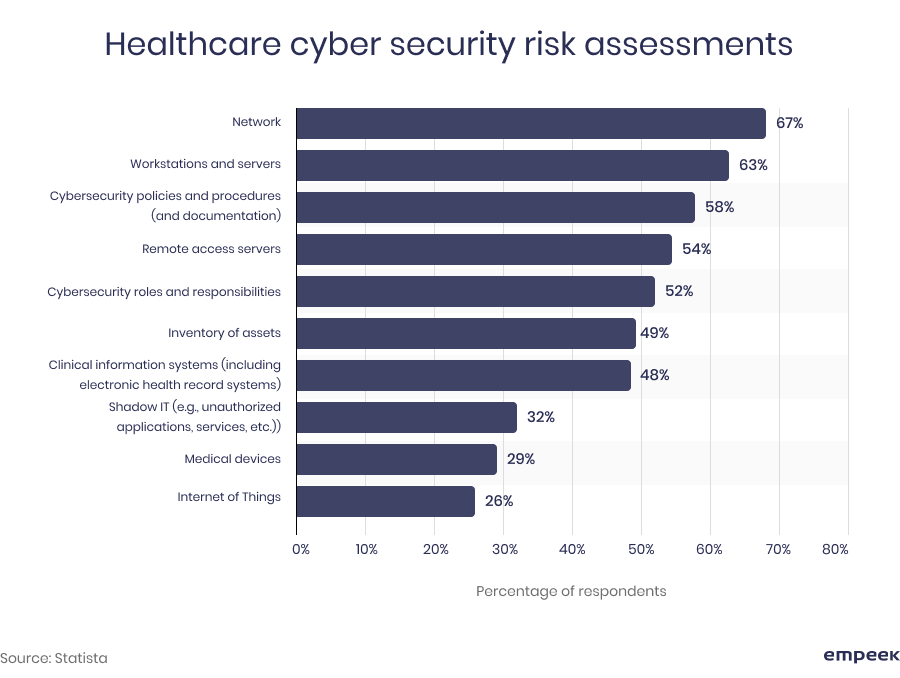
According to Statista, the main components through which healthcare organizations are exposed to various cyber risks include servers, intracompany networks, organizational websites, and clinical EHR systems. Let’s further review some of the most common cases below.
As you can see, in many cases, even an ordinary desktop computer that keeps an EHR database in the hospital’s registry or a unit of medical equipment can jeopardize the patient’s security. Data breaches, leakages, and other various privacy issues with electronic health records development can happen due to different reasons. The major categories of such threats are the following:
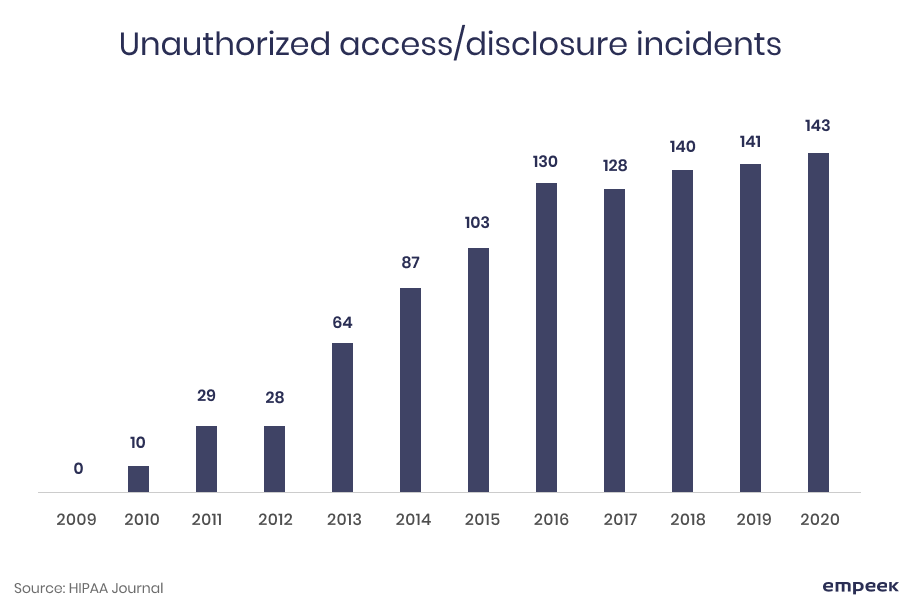
Violation of access privileges
Both morbid curiosity and malicious intent can stay behind the actions of some staff members who use their access permissions in the wrong way. This is about another sort of abuse of authority which, even though is unacceptable in a healthcare environment, might still take place if proper data protection measures are not set.
This is where two-factor authentication is a real life-savior. To ultimately reinforce the impenetrability of sensitive data, blockchain can be used. The blockchain data storing and protecting approach renders unauthorized data access attempts practically useless. Password encryption is another helpful initiative.
Fake authorization
EHR development security solutions are meaningless without advanced protection of data accessibility. If neither two-factor authentication nor password encryption is used to reach sensitive EHR data, some financial info such as billing data, credit card numbers, and insurance info can appear in the hands of the wrong person who might use the data to one’s advantage.
These and other EHR security and privacy issues can be efficiently solved and avoided with a good dose of automation, which can be achieved with IoT and AI-powered systems integration.
External network mismanagement
When a part of the EHR database leaves an intrahospital network for either cloud storage or some external networks, the vulnerability of EHRs increases significantly. When access to a clinic’s database can be enabled from somewhere outside the hospital premises, the privacy of EHR data is exposed to risk.
How to optimize such vulnerability? The answer is proprietary data storage and blockchain protection. Modern data storage solutions provide centralized next-generation protection and allow for reducing breach risks.
Human factor mistakes
People remain people no matter how advanced the technologies they use appear to be. There are a lot of ways to lose data through negligence: misaddressed emails, occasional data sharing with unauthorized persons, recovery of forgotten passwords with inappropriate methods, making screen data visible for foreign visitors, and many others.
Mentioned above IoT, AI, and blockchain integrations can help optimize the situation. A thorough staff monitoring added up with unrivaled blockchain data protection should certainly help eliminate tons of unnecessary errors.
Hackers and viruses
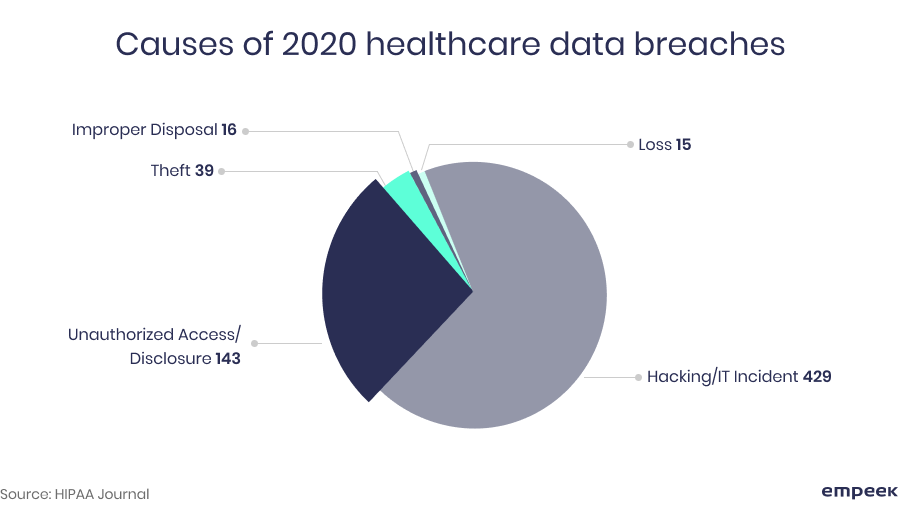
According to statistics, hacking attacks are the most widespread reason for data breaches in medical establishments. On top of that, cyber-criminals are constantly upgrading their techniques to steal confidential information. That’s why special attention should be paid to cybersecurity measures.
Electronic health records security and privacy concerns can unlikely go beyond the denial-of-service attacks and system viruses. The latter is aimed at encryption of critical EHR data to extort money from healthcare providers for decryption. For example, the infamous WannaCry ransomware started infecting thousands of computers around the world after the UK National Healthcare Service has been paralyzed by the virus.
Security Solutions in EHR Development
The above-mentioned categories of EHR security and privacy issues are threatening as such, but what makes them even more severe is their temporal aspect. In other words, it can take weeks and months to identify data breaches before some countermeasures are applied. That is why preventive EHR security should be closely considered.
The following practices and security features are strongly recommended to implement when the EHR security architecture is under development.
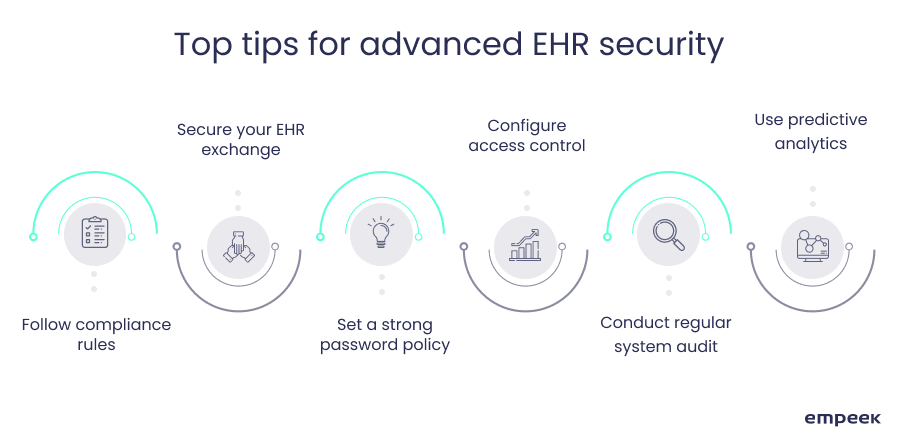
HIPAA Compliance
Following key security standards is crucial for any EHR development project. The standards are well-developed by the responsible governmental entities, and violation of the Healthcare Insurance Portability and Accountability Act (HIPAA) can entail significant penalties even if no security breach happens. It is worth studying the official HIPAA Compliance Checklist before security and privacy solutions in EHR development see the light.
To learn more about HIPAA regulations, read our article on HIPAA records retention requirements.
Secure EHR exchange
Protection of electronic document flows between all departments within a healthcare organization as well as between the organization and external entities is a must to avoid EHR data breaches. All potentially vulnerable communication channels should have encryption features to protect sensitive messages. Continually updated antivirus software is never optional for security solutions in EHR development as well.
Learn more about successful EHR implementation practices in our article.
Password protection
All messages from a healthcare institution to patients should be encrypted and accessible only with passwords. Two-factor authentication is another must-use method while changing the passwords.
The passwords should also be changed regularly. A special random password generator can be inbuilt in the system as an extra EHR development security solution to avoid setting too obvious passwords such as 12345678 or 11111111. Even though regular password resets may cause some inconvenience for patients and staff, the game is worth the candle when it comes to EHR security.
Access rights control
To avoid impermissible disclosure of EHRs, staff roles in the healthcare organization’s hierarchy should also be considered. The organization management should discuss how many levels of access the system is about to have and which staff belongs to each level. Automatic logoff could also be useful for the forgetful overworked staff.
Additionally, emergency moderator/sysadmin intervention option should be a part of the access control. Thus, when the system sends unauthorized access alerts, they can be promptly addressed and managed accordingly. Besides that, a special security feature should be in place to detect any sort of unusual or suspicious behavior within the system and notify the administrator immediately.
Regular system audit
Tracking all user activities in the system is necessary to detect possible data breaches in time. A pre-configured audit feature allows for monitoring a range of various parameters such as what data was accessed and when, who applied one’s authorization for data access, which devices/IP addresses were used, and other useful inputs.
Machine learning and deep learning technologies are able to suit security and privacy solutions in EHR development well. A regular audit report can be created with the help of AI-powered algorithms to facilitate automated generation and analysis of the reports.
Predictive analytics
AI-based predictive analytics working in a human-free mode can help detect unusual operational patterns in the system or identify the sensitive data that has been transmitted to an unauthorized recipient.
Predictive analytics engines can run 24/7 to accumulate and classify all suspicious cases. Therefore, it can work as a robust data leakage protection tool, which is essential for effective security solutions in EHR development.
Security in EHRs: Real-Life Cases
The years of experience in custom emr development made us a qualified advisor of security solutions in EHR development. We would like to share some best examples of making our customers’ data bulletproof.
Use Case #1. Security measures for emergency care

Real-time data sharing and cybersecurity risks often go hand in hand, but not on our watch. To ensure the highest level of protection for a medical emergency service provider, we created a web-based cross-platform app with such features as HIPAA compliance, two-factor authentication, encryption of healthcare information, and others. This allowed for secure data transmission and the elimination of potential data threats.
Use Case #2. Healthcare data security in EHR system

Another Empeek’s customer success case is replacing a 7 years old legacy EHR system for a US-based healthcare provider. The most up-to-date AI-powered data processing along with automated authentication made the system fully compliant with both HIPAA requirements and the zeitgeist of cyber-security.
We are proud of our partnership with various healthcare organizations that have entrusted us with making their electronic databases safe and secure. Discover more of Empeek’s success stories in our portfolio.
Final Thoughts
Various EHR privacy and security issues can unlikely disappear from the agenda of healthcare providers completely. They are the growing pains inherent in a paradigm shift from a paper standard to a digital one.
Human-factor negligence, access permission violations, obsolete authorization methods, hacking, and ransomware all belong to factors capable of compromising data privacy in EHRs. But all the threats are far from fatal if security solutions in EHR development are created with skill.
Contact us to get assisted in making your EHR system bullet-proof secure with the most up-to-date software development technologies.








